Cybersecurity, like money, is one of those things that become screamingly important when there is a lack of it. Compliance is widely recognised to be a critical component of cybersecurity. This article considers how an in-house counsel and other legal practitioners can support a corporate client in pursuit of better compliance in cybersecurity.
A number of large, well-publicised data breaches were reported in 2016–17. Some were the result of non-malicious employee error (for example the Commonwealth Department of Health’s publication of confidential information on its public portal), whilst others were the result of organised cyberespionage. An IT contract should provide for all eventualities.
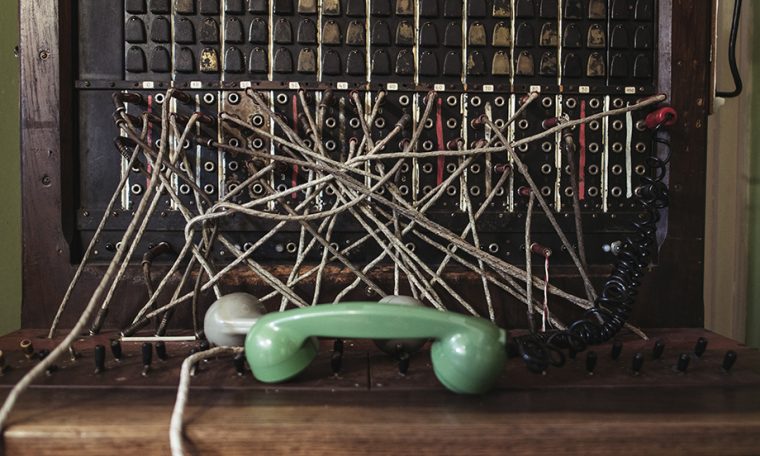
Technology contracts often deal with cybersecurity by imposing obligations and liabilities to keep networks, software and digital assets secure. The scale and significance of more recent data breaches has led to a new focus on supply chain security. Risks and vulnerabilities are more likely than ever to be introduced into your client’s technology by a malicious act, impacting not only their operations but those of their contractors, subcontracts, third party suppliers and so on.
In April 2017, security researchers published a report1 into a long-term international cyberespionage campaign. The security threat was dubbed ‘APT10’ and researchers released the report in order to raise awareness so that prevention and detection capabilities could be put in place. As commercial lawyers advising in technology deals, we should be aware of vulnerabilities such as APT10, and recognise that to some extent back-to-back agreements and contractual visibility of primary service providers and their main subcontractors may not adequately deal with today’s risks and the complex liability issues that arise.
APT10 impacted managed service providers in Australia, the UK, the USA, a number of north European nations, South Africa, India, Thailand and South Korea. However, Managed Service Providers (MSPs) were not the intended victims. MSPs were compromised in order to infiltrate the networks of their clients, covering a diverse field, including: engineering, manufacturing, retail, energy, pharmaceuticals, telecoms and government agencies. Interestingly, APT10 did not initially target mission critical technology. Malware was installed on non-critical machines, which were then used to move laterally into the targeted technology. Remote desktop protocols were used to steal data, which was then collated, compressed and sent from the MSP’s network to infrastructure controlled by APT10. It is worth noting that the security researchers indicated that they had observed APT10 since 2013. The report does not disclose how much data or the types of data that were compromised by APT10.
From a commercial lawyer’s perspective, at a basic level, cybersecurity is about trying to maintain confidentiality. At a more sophisticated level, a commercial lawyer can assist clients by fully understanding the commercial arrangement and helping the client to protect itself against a known cybersecurity risk.
If your client is involved in a data breach it is not only commercially sensitive information that will be compromised; they are likely to face the disclosure of personal information affecting hundreds of thousands – if not millions – of people. In the face of high reputational risk and other liabilities, a well-constructed commercial deal containing a clear framework with agreed rights, roles and liabilities can go a long way towards (ideally) preventing as far as possible a cyberattack, and minimising its impact should one occur. While transfer of risk is a valid risk minimisation strategy, it is not possible to contract out of regulatory data protection and data compliance obligations.
Issues for consideration when drafting or negotiating contracts:
Definition of confidential information
- It would be prudent for a customer to insist on a detailed and ‘including but not limited to’ list in the definition of confidential information, for example:
- data
- personal information (including sensitive information)
- medical information
- financial information.
- An IT supplier would be better served if the customer accepted a more traditional definition of confidential information, limited to material that the customer clearly communicates to be confidential, and expressly not including any material made by the IT supplier or its subcontractors.
- Definitions for personal and sensitive information can be tied to the Privacy Act 1988 (Cth) and its attendant Australian Privacy Principles.
- It is good practice to separately define confidential information for both the parties, as each party will share a different type of information during the performance of the contract, and each party will have a different role for data transmission, data storage and data ownership. If there is only a one way flow of information, only one party’s information should be protected.
Contractual obligation to maintain confidentiality
- Agreements should contain obligations not to disclose and not to misuse information. It is common for a confidentiality obligation to survive expiry or termination for a set period of time. Perpetual protection of confidentiality should be drafted carefully, noting there is case law that suggests that such clauses will be read down to apply only until the confidential information has entered the public domain.2
- The clause should describe what should happen to the confidential information at the expiry or early termination of the contract. For example, is the provider permitted to retain a copy? Must all confidential information be returned or destroyed (and at the election of which party)?
- A separate positive obligation should also be included to stipulate that no information/data is released either to a third party or to the world at large.
Notification obligation
- A contract should include a separate positive obligation to promptly report any security breach affecting the customer’s data to the other party. Without such an obligation, there may be a long delay in responding to the data breach and a party becoming aware that their information has been compromised.
- A customer might wish to include an obligation to be informed upon any data breach (i.e. even a data breach not affecting the customer’s data).
- Ideally, the contract should raise an obligation to notify the other party of any actual or suspected data breach within two business days, remembering that time is of the essence in addressing commercial, operational, reputational and regulatory issues that arise. From 22 February 2018 obligations pursuant to the new Notifiable Data Breaches regime must also be factored in.
Service levels
- A contract should contain service levels that bring metrics to a failure to perform cybersecurity measures.
- Service levels could support obligations to comply with a customer’s security standards and data security obligations pertaining to personal information that arise pursuant to regulatory provisions.
Note that if a data breach is the supplier’s fault, the customer may have a common law action for breach of confidence available. Such an action could lead to an award of damages, an accounting of profits, a constructive trust, injunctive relief or restitution, for example:
Both parties should conduct due diligence on how data will flow from one party to another
- It should be possible to identify the main risks of how a data breach can occur. You should encourage your client to identify what information is at risk and the pathways of information flow (not only between the parties, but if you are advising the IT supplier, the pathways through which the customer’s information flows within their organisation and also to subcontractors).
- An IT supplier should have in place internal measures and controls to track information flows and their compliance with confidentiality and regulatory obligations.
- Information storage issues should be considered, for both storage in software and storage in equipment.
- If you are advising a customer and your client is concerned about data breach, you should consider negotiating bespoke contractual provisions describing what is permitted and what is not permitted in relation to data storage, use and transmission.
Liability
Should your organisation or client then be affected by a data breach (either as a victim, as an organisation targeted by a hacker or as an organisation that has subcontracted where the subcontractor is the target of a cyber attack) the contractual framework should be clear. Most importantly, the contractual framework should clearly describe each party’s obligations in relation to a data breach, notification steps, timelines, which party is responsible, liability and the handling of claims by third parties.
Indirect/consequential loss
Loss of data is becoming an increasingly contested negotiation point in the context of indirect/consequential loss. While it is not uncommon for indirect/consequential loss to be excluded from an agreement, we recommend close consideration be given to treatment of data (and loss of data). Where relevant, loss of data should be expressly acknowledged to be a direct loss, so as not to be captured in any exclusion of indirect/ consequential loss. There is always middle ground which can be negotiated, such as treating loss of data as a direct loss only if agreed security measures and data back-up systems are implemented to limit the risk of loss to data.
Subcontractors
From a customer perspective, consider negotiating a limitation on the supplier’s ability to subcontract and require prior written approval. If a customer has the right to give their approval prior to subcontracting, there is an opportunity for the customer to vet subcontractors from a cybersecurity perspective.
Additional provisions for consideration
- Require individual contractor and subcontractor’s personnel to execute undertakings in respect of security or access to customer premises
- Obligation for personnel (contractor and subcontractor personnel) to undergo security assessment
- Obligation for personnel (contractor and subcontractor personnel) to attend your security training.
Rights to access and audit
Even if a technology contract does not give a third party the right to access your client’s information, many practitioners also look to include an unfettered contractual right for the owner of the data to conduct independent checks of the security measures in place. You should also consider the terms of technology contract to ensure that your client will not be in breach of contract if they decide in the future to engage a third party to monitor the technology to ensure a supplier’s staff or a third party are not stealing or making unauthorised modifications to your data.
Insurance
Cyber insurance will afford an additional level of protection should an adverse event arise. Once again though, the agreement should identify who is responsible for taking out insurance and for what, also considering whether the interests of other parties should be noted.
At the end of the day, compliance is a level of protection but not a guarantee of security. Compliance as a line of defence will only be as strong as your weakest link. In that context, the supply chain and procurement practices represent risks often not identified when the compliance focus is inward facing. Cyberspace represents a clear and ever present danger to organisations of all types and sizes, so don’t let your client’s weakest link be their downfall.
This article was first published in Australian Corporate Lawyer, Autumn 2018 and is reproduced with permission.
This memo presents an overview and commentary of the subject matter. It is not provided in the context of a solicitor-client relationship and no duty of care is assumed or accepted. It does not constitute legal advice.
© Moulis Legal 2018
[1] Operation Cloud Hopper—exposing a systematic hacking operation with an unprecedented web of global victims, April 2017, www.pwc.co.uk/cyber.
[2] Maggbury Pty Ltd v Hafele Australia Pty Ltd (2001) 210 CLR 181.